The Essential Before & After Guide (Avoid Breaking Your System!)
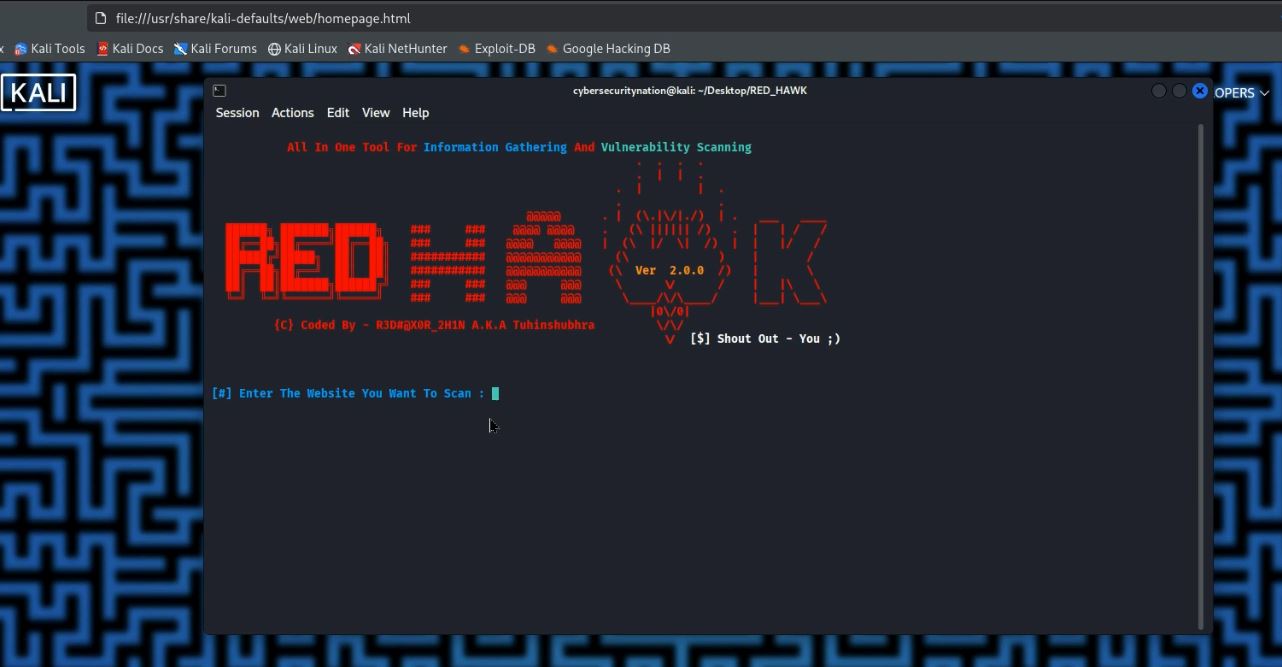
Welcome, ethical hackers and cybersecurity enthusiasts! If you’re stepping into the world of penetration testing, you’ve likely heard about Kali Linux. It’s the go-to operating system packed with powerful tools for cybersecurity professionals. But getting your Kali Linux environment set up correctly, especially within a Virtual Machine (VM), can be tricky. Many beginners often face frustrating issues – from slow performance to “broken” systems – simply by missing a few crucial steps.
Fear not! At Cybersecurity Nation, we’re here to guide you. This comprehensive Kali Linux VM setup guide will walk you through everything you need to do before and after installing Kali Linux in your virtual environment. By following these steps, you’ll avoid common pitfalls, ensure optimal performance, and build a stable platform for your ethical hacking journey. Let’s get started and set up your secure hacking lab without the headaches!
Before You Install Kali Linux: The Crucial Preparations
The success of your Kali Linux VM installation heavily relies on the groundwork you lay beforehand. Skipping these initial steps is a common reason why virtual machines behave unexpectedly or fail to perform optimally.
1. Enable Virtualization Technology (VT-x / AMD-V) in Your BIOS/UEFI
This is arguably the most critical step. Your computer’s processor needs to have virtualization technology enabled for your VM software (like VirtualBox or VMware) to function efficiently. Without it, you might experience extremely slow performance, or your VM might not even start.
- How to Enable Virtualization:
- Reboot your PC.
- As it restarts, repeatedly press the key to enter your BIOS/UEFI settings. This key varies by manufacturer but is commonly F1, F2, Del, Esc, or F10.
- Once in the BIOS/UEFI menu, navigate to settings related to CPU Configuration, Processor, System Configuration, or Advanced Settings.
- Look for an option named “Virtualization Technology”, “Intel VT-x”, “AMD-V”, or similar.
- Enable this option.
- Save your changes (usually by pressing F10) and exit the BIOS/UEFI to restart your computer.
Note: The exact menu names and key presses may differ slightly based on your PC’s brand (HP, Dell, Lenovo, Asus, Acer, etc.) and BIOS version. Consult your motherboard’s manual if you’re unsure.
2. Download Essential Software: Virtual Machine and Kali Linux ISO
Once virtualization is enabled, you’re ready to get the necessary software.
- Virtual Machine Software (Hypervisor):
- For most beginners, Oracle VirtualBox is an excellent free and open-source choice. Download the latest version for your host operating system from: virtualbox.org
- Alternatively, VMware Workstation Player (free for non-commercial use) or VMware Workstation Pro (paid) are popular robust options: vmware.com
- Kali Linux ISO Image:
- Always download the official Kali Linux ISO from the source to ensure authenticity and avoid compromised images. Visit: kali.org/get-kali/
- Choose the appropriate 64-bit or 32-bit version for your needs. For most modern systems, the 64-bit installer image is recommended.
3. Configure Your Virtual Machine Settings
Before you even start the Kali Linux installation process, you need to create and configure your new virtual machine.
- Resource Allocation (RAM, CPU, Disk Space):
- RAM: Allocate at least 2GB of RAM to your Kali Linux VM for basic operation. For smoother performance or running multiple tools, 4GB is ideal if you have atleast 16GB of host system’s total RAM. Do not allocate more than half of your host system’s total RAM.
- CPU: Assign at least 2 processor cores. This significantly improves responsiveness. Again, this depends on your system specification.
- Disk Space: Allocate a minimum of 20-30GB for the virtual hard disk. This allows for Kali’s default tools and future updates/installations.
- Network Settings (NAT vs. Bridged Adapter):
- NAT (Network Address Translation): This is the default and simplest option. Your VM gets its IP address from the VM software, which then “translates” its requests through your host’s network. It’s generally safer as the VM is somewhat isolated from your local network.
- Bridged Adapter: This option makes your VM a full participant on your physical network, getting its IP address directly from your router, just like your host machine.
- Recommendation for ethical hacking: For many penetration testing scenarios where you need your Kali VM to communicate directly with other devices on your local network (e.g., scanning other machines), Bridged Adapter is often preferred. This ensures your VM is on the same IP range as your host OS and other network devices.
- To set this in VirtualBox: Go to VM Settings -> Network -> Adapter 1 -> Attached to: “Bridged Adapter” -> Select your active host network interface.
During Installation Tips: Smart Choices for a Smooth Setup
Once your VM is configured and the Kali ISO is attached, you’ll begin the installation process. Here are a few key points:
- Graphical Install: Choose the “Graphical install” option for an easier, guided setup.
- User Account: Create a non-root user account and set a strong password. Avoid using root as your primary daily user for security best practices.
- Disk Partitioning: For beginners, “Guided – Use entire disk” is perfectly fine. Kali will automatically set up partitions for you.
- Network Configuration: Ensure your network (wired or wireless) is detected and configured. This is where your earlier network settings in the VM come into play.
Post-Installation Checklist: Optimizing Your Kali Linux VM
Congratulations! Kali Linux is installed. Now, these critical post-installation steps will make it functional, secure, and ready for action.
1. Update & Upgrade Your System
This is non-negotiable for security and access to the latest software.
sudo apt update
sudo apt upgrade -y
sudo apt dist-upgrade -y- sudo apt update: Refreshes the list of available packages.
- sudo apt upgrade -y: Installs the newer versions of all currently installed packages. The -y flag answers “yes” to all prompts.
- sudo apt dist-upgrade -y: Handles package changes more intelligently, installing new packages or removing old ones to satisfy dependencies.
Always perform a system reboot after major upgrades: sudo reboot
2. Install Virtual Machine Tools (Guest Additions / VMware Tools)
These tools are crucial for better integration between your host and guest OS. They provide:
- Better display resolution and dynamic resizing
- Shared clipboard functionality
- Drag-and-drop file transfer
- Seamless mouse integration
- Improved overall performance
- For VirtualBox (Guest Additions):
- With your Kali VM running, go to the VirtualBox menu bar: Devices > Insert Guest Additions CD Image
- Open your Kali Linux terminal and navigate to the mounted CD-ROM:
cd /media/cdrom0/3. Run the installation script:
sudo sh VBoxLinuxAdditions.run4. You might get an error if linux-headers are missing (covered below). After successful installation, reboot your VM.
- For VMware (VMware Tools):
- With your Kali VM running, go to the VMware menu bar: VM > Install VMware Tools.
- Follow the on-screen prompts or the installation steps similar to VirtualBox (mount the virtual CD, extract the archive, and run the installation script).
- Reboot your VM.
3. Set Up User Accounts and Basic Security Practices
- Non-Root User: As mentioned, use your non-root user account for daily tasks. Only use sudo for administrative commands.
- Strong Passwords: Ensure all user accounts have strong, unique passwords.
- SSH (Optional but Recommended): If you plan to remotely connect to your Kali VM, enable and secure SSH. Change the default port and consider key-based authentication.
4. Customize Your Terminal and Environment
Personalization makes your workflow more efficient and enjoyable.
- Terminal Theme: Change colors, fonts, and transparency.
- Shell Customization (Bash/Zsh): Install zsh and Oh My Zsh (https://ohmyz.sh/) for powerful auto-completion, themes, and plugins.
- Install Preferred Tools: Add any additional tools not included in your default Kali installation.
Avoiding Common Pitfalls: Fixing Linux-Headers Errors
One of the most frequent errors users encounter, especially when trying to install Guest Additions or other kernel-dependent software, is related to missing or mismatched linux-headers. These headers are crucial files that match your Linux kernel version, allowing external modules (like VM tools) to compile correctly.
Solving linux-headers Errors:
If you receive an error about linux-headers during Guest Additions installation, follow these steps:
- Check Your Current Kernel Version:
uname -rThis command will show you the exact version of your running Linux kernel.
- Ensure Your System is Fully Updated:
sudo apt update
sudo apt dist-upgrade -yAlways run dist-upgrade to ensure your kernel is the latest version available through Kali’s repositories.
- Reboot Your VM:
sudo rebootThis ensures you are running on the newly updated kernel, if one was installed.
- Verify New Kernel Version (Optional, but good practice):
After reboot, run uname -r again to confirm you are on the latest kernel. - Install the Correct Linux Headers:
Now, install the headers that precisely match your current running kernel version:
sudo apt install -y linux-headers-$(uname -r)The $(uname -r) part automatically plugs in your current kernel version into the command.
- Reinstall VirtualBox Guest Additions:
After successfully installing the linux-headers, you can now proceed to reinstall Guest Additions.- Ensure the Guest Additions CD Image is still inserted in VirtualBox (Devices -> Insert Guest Additions CD Image).
- Navigate to the mounted CD-ROM in your terminal:
cd /media/cdrom0/- Execute the installation script:
sudo sh VBoxLinuxAdditions.runReboot your VM one last time for the changes to take full effect.
Safeguarding Your Setup: The Power of Snapshots
You’ve put in the effort to configure your Kali Linux VM perfectly. Now, imagine accidentally breaking something crucial while experimenting with an ethical hacking tool or a new configuration. It happens to the best of us! That’s where VM snapshots become your cybersecurity superpower.
What are Snapshots and Why are They Crucial for Ethical Hacking?
A snapshot is like taking a photo of your virtual machine’s entire state at a specific moment in time. This includes its files, settings, and the running operating system. If something goes wrong later, you can instantly “roll back” to that saved snapshot, effectively undoing any problematic changes.
For an ethical hacking lab, snapshots are invaluable because they:
- Prevent Reinstallation Headaches: No need to reinstall Kali Linux from scratch if you make a mistake or a tool breaks your system.
- Facilitate Experimentation: You can freely test new tools, configurations, or even malware samples (in an isolated environment, of course!) knowing you can revert if needed.
- Save Time: Rolling back to a previous state takes minutes, compared to hours of reinstallation and reconfiguration.
How to Take a Snapshot (General Steps for VirtualBox/VMware)
The exact steps vary slightly between VirtualBox and VMware, but the concept is the same:
- Ensure your VM is in a desired, stable state (e.g., after all updates and Guest Additions are installed).
- Either shut down the VM or pause it. (Taking a snapshot while running is possible but shutting down is often more stable for major points).
- In your VM software’s main interface (e.g., VirtualBox Manager or VMware Workstation Player):
- Select your Kali Linux VM.
- Look for a “Snapshots” tab or menu option.
- Click “Take Snapshot” or “Create Snapshot.”
- Give it a clear, descriptive name (e.g., “Kali Linux Clean Install – Post Updates & Tools”) and add a brief description.
For a detailed walkthrough on creating, managing, and restoring VM snapshots, check out our dedicated video tutorial right here on the Cybersecurity Nation YouTube channel!
Before we conclude this tutorial, remember to take a snapshot of your current, working state of your VM. This ensures that if you mistakenly break your VM during your ethical hacking course, you can always roll back to a stable, working snapshot. It will save you immense time and frustration from having to uninstall and reinstall Kali Linux all over again!
- Conclusion: Your Robust Kali Linux Hacking Lab Awaits!
By diligently following these steps before and after installing Kali Linux in a VM, you’ve laid a strong foundation for your ethical hacking and cybersecurity learning. You’ve enabled virtualization, configured your VM resources, chosen optimal network settings, and proactively tackled common installation and post-installation issues like linux-headers errors.
This robust and stable Kali Linux virtual machine will serve as your reliable environment for exploring penetration testing tools, practicing your skills, and staying ahead in the ever-evolving world of cybersecurity. Happy hacking!
Don’t let your friends struggle with Kali Linux VM setup! Share this guide with them. If you found this tutorial helpful, please LIKE this post and let us know in the comments below what other Kali Linux or ethical hacking topics you’d like us to cover!






Leave a Reply