-
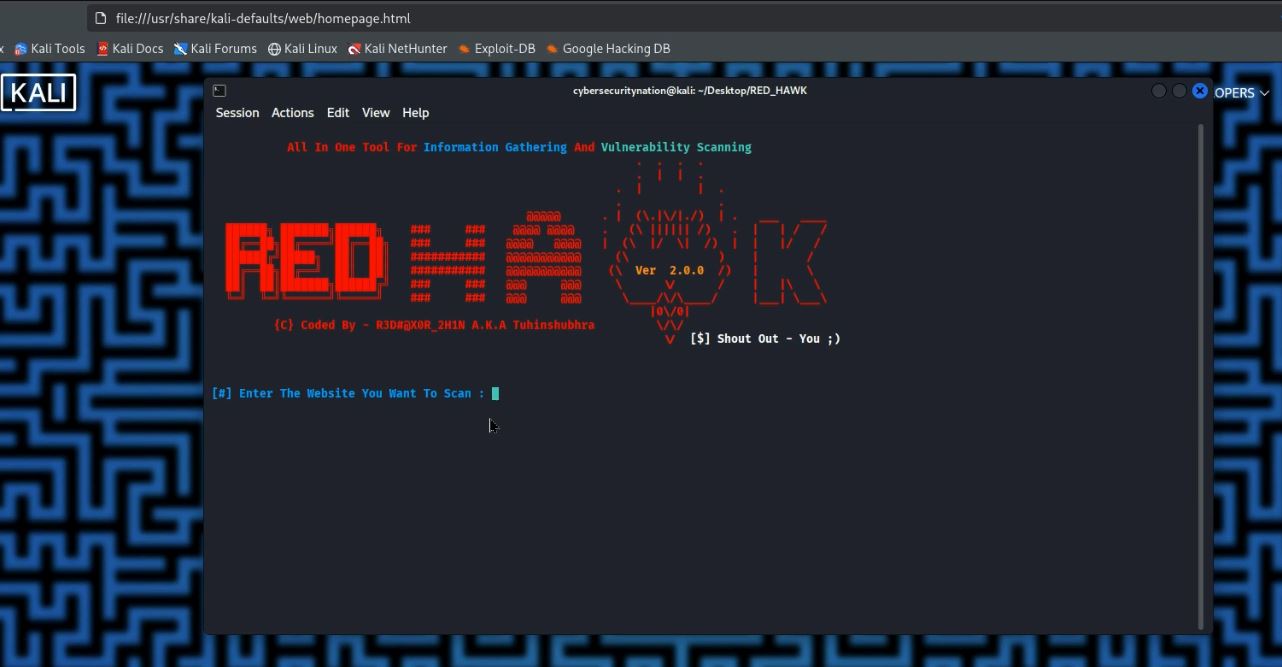 Continue reading →: How to Extract Emails and Usernames on Ethical Hacking Lab
Continue reading →: How to Extract Emails and Usernames on Ethical Hacking Labextract emails usernames osint tools
-
 Continue reading →: Before and after installing Kali Linux
Continue reading →: Before and after installing Kali LinuxMaster your Kali Linux VM setup! This essential guide covers crucial steps before and after installation, from enabling virtualization to fixing common errors. Avoid system breaks and optimize your ethical hacking lab.
-
 Continue reading →: First Hacking Lab: Install VirtualBox & Kali Linux
Continue reading →: First Hacking Lab: Install VirtualBox & Kali LinuxLearn how to download and install Oracle VirtualBox and Kali Linux step-by-step. Build your first ethical hacking lab safely, master VM setup, and begin your cybersecurity journey with this comprehensive guide.
-
 Continue reading →: What is Ethical Hacking? Your Guide to Cyber Defense
Continue reading →: What is Ethical Hacking? Your Guide to Cyber DefenseDiscover what ethical hacking is, how white hat hackers secure systems, and the difference from black hat hackers. Learn the role of penetration testers in cybersecurity defense and how to legally practice ethical hacking skills.
-
 Continue reading →: Data Breach: Your Guide to Recovery
Continue reading →: Data Breach: Your Guide to RecoveryHave you ever received a notification that your data might have been compromised? Understanding what a data breach is and knowing precisely what to do after your information has been leaked is crucial in today’s digital world.
Hello,
Hello!

Welcome to Cybersecuritynation.com, your premier hub for professional security training. Explore our free ethical hacking courses on this blog and our YouTube channel, @cybersecurenation. We provide exclusive free tools and expert tutorials on Python coding for security. Subscribe today to master the digital frontier and protect the future.
Let’s connect
Join the fun!
Stay updated with our latest tutorials and ideas by joining our newsletter.




