In the complex and often shadowy world of cybersecurity, there are heroes working tirelessly behind the scenes. These are the ethical hackers, the “good guys” who use their advanced technical skills not for malice, but for protection. If you’ve ever heard the term “hacking” and wondered if it could ever be a force for good, then you’re about to discover the fascinating and vital field of ethical hacking.
At CybersecurityNation.com, we believe that understanding the tools and techniques of both offense and defense is crucial for robust security. This guide will clarify what ethical hacking is, demystify the role of an ethical hacker, distinguish them from malicious actors, and provide insight into how you can legally develop these invaluable cybersecurity defense skills.
Ethical Hacking: The Cyber Police of the Digital World
Imagine a world where the only people who knew how to pick a lock were criminals. Our homes and businesses would be in constant peril. The digital world is much the same. If only the “bad guys” understood how to break into computer systems, our data, privacy, and infrastructure would be perpetually at risk. This is where ethical hacking comes in.
Ethical hacking, often referred to as penetration testing or white hat hacking, is the practice of attempting to breach a computer system, application, or network with the explicit permission of its owner. The goal is to identify vulnerabilities and weaknesses that a malicious attacker (a black hat hacker) could exploit. Once discovered, these vulnerabilities are reported to the owner, who can then patch them before they cause harm.
Think of ethical hackers as the “Cyber Police.” We are hired to test the defenses, expose the weak points, and help secure the target system. Our mission is to protect, not to exploit.
What Does an Ethical Hacker Do?
An ethical hacker, also known as a White Hat Hacker, operates with integrity and a clear ethical code. Their primary objective is to find as many vulnerabilities within a target system as possible. But what exactly constitutes a “system” and a “vulnerability”?
- A “System” Can Be Anything Digital: When we talk about a system, we’re referring to any digital asset that needs protection. This could include:
- Networks: A collection of multiple interconnected computers within an organization.
- Individual Computers/Devices: A single workstation, server, or mobile device.
- Company Servers and Databases: Crucial infrastructure holding sensitive data like customer records, financial information, or intellectual property.
- Websites and Web Applications: E-commerce platforms, company portals, or online services that might have exploitable bugs.
- Cloud Environments: Infrastructure and applications hosted in cloud services.
- A “Vulnerability” Is a Weak Point: A vulnerability is essentially any flaw, weakness, or misconfiguration in a system that could allow an unauthorized person to gain access, steal data, or disrupt operations. This could be anything from outdated software, weak passwords, faulty configurations, or even human error. Ethical hackers are there to discover these chinks in the digital armor and report them.
Their work is proactive, simulating real-world attacks to strengthen defenses before real damage occurs. This is a critical component of modern information security and network security.
White Hat vs. Black Hat: The Critical Difference
The methods used by White Hat and Black Hat hackers can often be quite similar. Both use tools and techniques to probe for weaknesses. However, their intentions and legal standing are fundamentally different:
- White Hat Hackers (Ethical Hackers):
- Goal: To find vulnerabilities and report them to the owner to improve security.
- Permission: ALWAYS operate with explicit, written permission from the system owner.
- Legality: Their actions are legal and ethical.
- Outcome: Enhanced security, patched systems, protected data.
- Role: Security consultant, penetration tester, cyber defense expert.
- Black Hat Hackers (Malicious Hackers):
- Goal: To find vulnerabilities to exploit them for personal gain, destruction, or disruption.
- Permission: NEVER operate with permission; their actions are unauthorized.
- Legality: Their actions are illegal and unethical, often leading to severe legal consequences.
- Outcome: Data theft, financial fraud, system damage, privacy invasion, installation of malware (e.g., viruses, keyloggers to track activity), or even identity theft.
- Role: Cybercriminal, malicious actor.
This distinction is paramount. A White Hat Hacker is a protector, using their skills to build resilience against those who seek to cause harm. They are an integral part of cyber defense strategies for businesses, governments, and individuals.
The Ethical Hacker’s Methodology: Attacking to Defend
How does an ethical hacker achieve their goal of securing systems? By attacking them – but with a different goal in mind. They essentially “act as a Black Hat Hacker” to uncover the same weaknesses a malicious actor would exploit.
An example scenario might involve a company hiring an ethical hacker to assess their security posture. The hacker would then:
- Scope the Target: Understand the company’s assets – their website, internal networks, employee computers, large servers, and databases holding critical company data.
- Information Gathering: Collect as much public and non-public information about the target as possible, just as an attacker would.
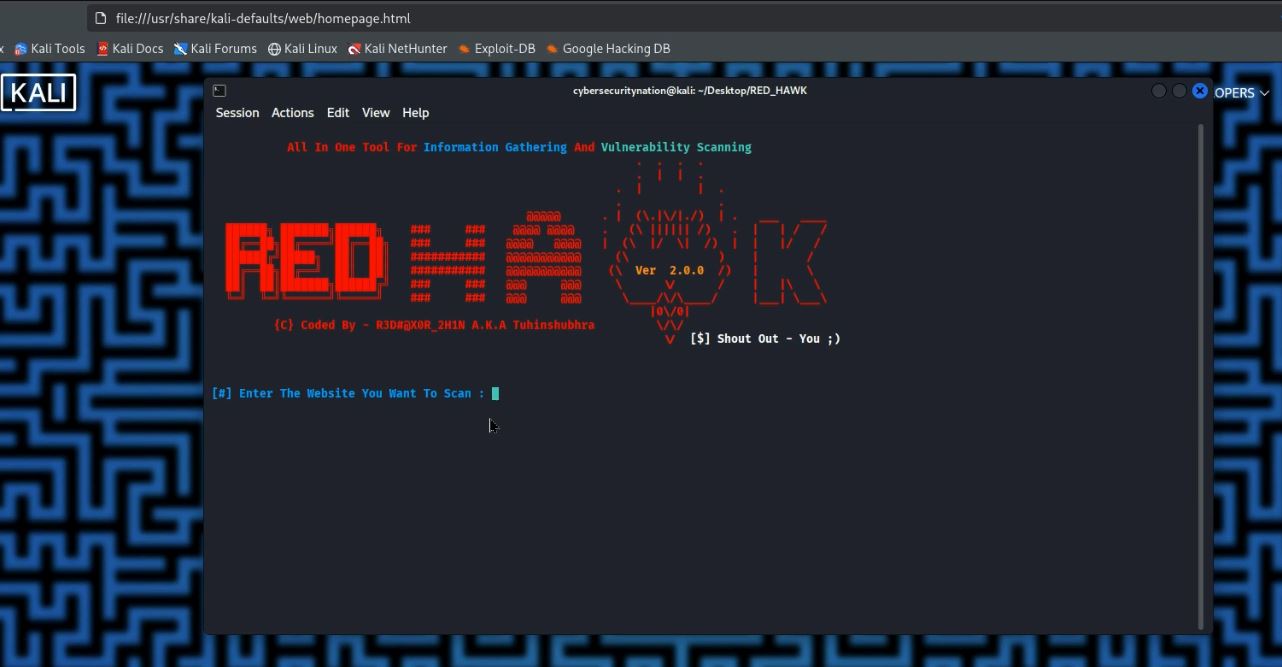
- Vulnerability Scanning: Use specialized tools to scan for known weaknesses in networks, operating systems, and applications.
- Exploitation (Controlled): Attempt to exploit identified vulnerabilities to demonstrate potential impact, but without causing real damage or exfiltrating sensitive data. This might involve attempting to breach a company’s website for bugs, test network security for employees’ machines, or probe database defenses.
- Reporting: Provide a detailed report of all discovered vulnerabilities, their potential impact, and recommendations for remediation.
- Remediation & Re-testing: The company then fixes the issues, and sometimes the ethical hacker performs a re-test to confirm the vulnerabilities are patched.
This systematic approach, known as a penetration test, helps organizations understand their real-world risk and significantly improve their cybersecurity posture.
Learning Ethical Hacking Legally and Ethically
The ethical imperative of “permission” can raise questions about how one learns and practices ethical hacking skills. Don’t worry, breaking the law is never required to become a skilled ethical hacker.
We simulate all these targets in controlled environments. This typically involves:
- Home Devices & Virtual Machines: Setting up your own network of computers (physical or virtual) on your home network. See how to install Virtual Machines.
- Virtualization Software: Using tools like VirtualBox or VMware to create virtual machines (VMs). These VMs can host various operating systems (like Kali Linux for hacking tools, and vulnerable systems like Metasploitable) that you can legally and safely practice attacking.
- Capture The Flag (CTF) Challenges: Participating in online security competitions designed to test hacking skills against intentionally vulnerable systems. You can join tryhackme to practice your skills.
- Bug Bounty Programs: Legitimate programs run by companies that pay ethical hackers to find and report vulnerabilities in their live systems.
By practicing in these safe, legal environments, you develop the expertise needed to become a master in ethical hacking without ever compromising real-world systems illegally. You learn the attack methods by setting up your own targets, making sure you won’t be breaking any law while you practice, since the target that you will attack will be yours.
One of the biggest online cyberattacks often explored in this field is phishing, where black hat hackers trick individuals into revealing private data like usernames and passwords. Understanding how phishing works, even by simulating it in a controlled environment, helps ethical hackers advise on stronger security awareness.
Conclusion
Ethical hacking is a dynamic and essential field within cybersecurity. It’s about leveraging technical prowess for the greater good – to safeguard digital assets, protect privacy, and build a more secure online world. By understanding the mind of an attacker and proactively identifying weaknesses, ethical hackers serve as critical guardians in the ongoing battle against cybercrime. Their work ensures that the digital future remains secure for everyone.
For more information on cybersecurity and ethical hacking concepts, delve into reputable resources from security organizations and educational platforms.
What aspects of ethical hacking intrigue you the most? Do you see yourself as a future white hat hacker? Share your thoughts and questions in the comments below! And if you found this guide insightful, please like and share it to help spread awareness about the importance of ethical hacking in our digital defense!







Leave a Reply