What is a Man-in-the-Middle (MITM) Attack?
A man-in-the-middle attack is a cybercrime where hackers secretly intercept and manipulate communication between two parties, like eavesdropping on a private conversation. Imagine a postal worker opening your bank statement, copying your details, and resealing the envelope—MITM works similarly. Attackers steal login credentials, financial data, or even hijack sessions to impersonate users.
Why It’s Dangerous:
- Targets financial apps, e-commerce sites, and SaaS platforms.
- Enables identity theft, fraud, or Advanced Persistent Threats (APTs).
- Leaves no trace, making detection difficult.
What is a Man-in-the-Middle (MITM) Attack? A man-in-the-middle attack is a cybercrime where hackers secretly intercept and manipulate communication between two parties, like eavesdropping on a private conversation. Imagine a postal worker opening your bank statement, copying your details, and resealing the envelope—MITM works similarly. Attackers steal login credentials, financial data, or even hijack sessions to impersonate.
How MITM Attacks Work: Interception & Decryption
MITM attacks unfold in two phases:
1. Interception
Attackers position themselves between victims using:
- Fake Wi-Fi Hotspots: Free, unsecured networks in public places (e.g., “Starbucks_WiFi_Free”).
- Spoofing:
- ARP Spoofing: Forges MAC addresses to redirect traffic.
- DNS Spoofing: Hijacks DNS servers to send users to fake sites.
- IP Spoofing: Masquerades as a trusted IP address.
2. Decryption
Once intercepted, attackers decrypt sensitive data using:
- HTTPS Spoofing: Fake SSL certificates mimic trusted sites.
- SSL Stripping: Downgrades HTTPS connections to unsecured HTTP.
- SSL BEAST: Exploits TLS vulnerabilities to steal encrypted cookies.
Real-World MITM Attack Examples
- The 2020 Twitter Bitcoin Scam: Hackers used MITM tactics to breach employee accounts, posting fraudulent Bitcoin tweets from Elon Musk and Barack Obama.
- Public Wi-Fi Eavesdropping: Attackers at airports intercept unencrypted sessions to steal credit card details.
- Banking Trojan Malware: Malware like Zeus uses MITM to hijack online banking sessions.
How to Spot a MITM Attack
Watch for these red flags:
- Browser Warnings: “Site Not Secure” or certificate errors.
- Slow Network Speeds: Unusual lag on “secure” connections.
- Mismatched URLs: Slight typos like “faceb00k-login.com.”
6 Steps to Prevent MITM Attacks
- Use HTTPS Everywhere: Install browser extensions like HTTPS Everywhere.
- Avoid Public Wi-Fi: Never access banks or emails on unsecured networks.
- Enable VPNs: Encrypt traffic with tools like NordVPN.
- Update Software: Patch OS and browsers to fix vulnerabilities.
- Deploy Multi-Factor Authentication (MFA): Adds a layer beyond passwords.
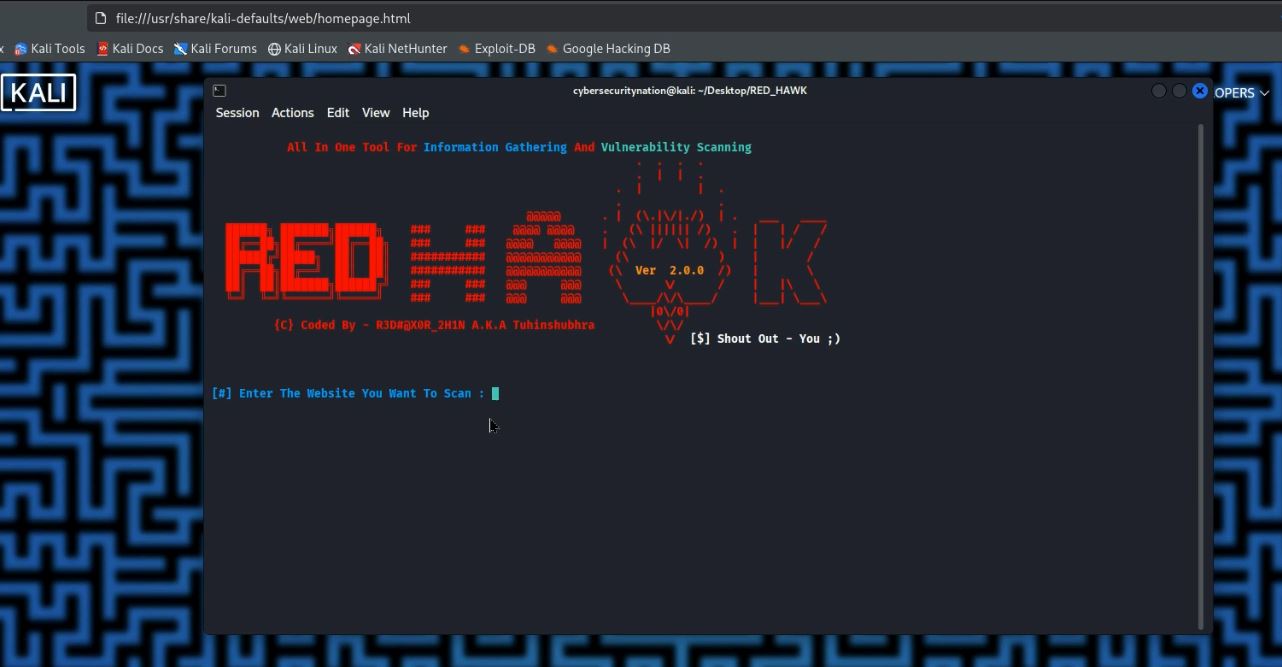
- Monitor ARP Tables: Use tools like Arpwatch to detect spoofing.
Pro Tip: Bookmark NCSC’s Phishing Guide for free cybersecurity resources.
MITM Prevention for Website Owners
- Implement HSTS: Force HTTPS with HTTP Strict Transport Security.
- Validate SSL/TLS Certificates: Use trusted authorities like Let’s Encrypt.
- Encrypt All Pages: Don’t limit SSL/TLS to login pages.
FAQ: MITM Attacks
Q: Can HTTPS fully prevent MITM attacks?
A: HTTPS encrypts data, but attackers can still use fake certificates. Pair it with HSTS and certificate pinning.
Q: What’s the most common MITM attack?
A: ARP spoofing on unsecured LANs.
Q: Are mobile devices at risk?
A: Yes! MITM targets LTE, Bluetooth, and malicious apps.
Final Thoughts MITM attacks exploit trust in digital communication, but awareness and encryption are your best defenses. Always verify URLs, use VPNs, and stay skeptical of “too-good-to-be-true” Wi-Fi.
Reference
Mallik, A., Ahsan, A., Shahadat, M. M. Z. and Tsou, J. C. (2019) ‘Man-in-the-middle-attack: Understanding in simple words’, International Journal of Data and Network Science, 3(2), pp. 77–92.







Leave a Reply